Have you ever looked ate your electric bill and noticed it has a nice monthly readout of usage? Wouldn’t it be great to get that same data in Aria Operations and even be able to set alerts on it? Well now you can. In this guide I will show you how to collect egress data from VMC on AWS and send it over to an Aria Operations dashboard.
Pre-Reqs
- VMC on AWS SDDC deployed and configured to allow Compute network access to the internet
- One Linux VM deployed that will run your scripts, I am using CentOS 7, here is a list of OS’s supported for Telegraph Agent.
- Aria Operations deployed and Cloud proxy deployed and configured to point to the SDDC vCenter
- Firewall rules open from the Cloud Proxy to the ESXi hosts in the SDDC, this is so the Cloud Proxy can communicate with the Linux VM running the agent
- A token from CSP portal with permission to read ORG details and access to read NSX details see guide here
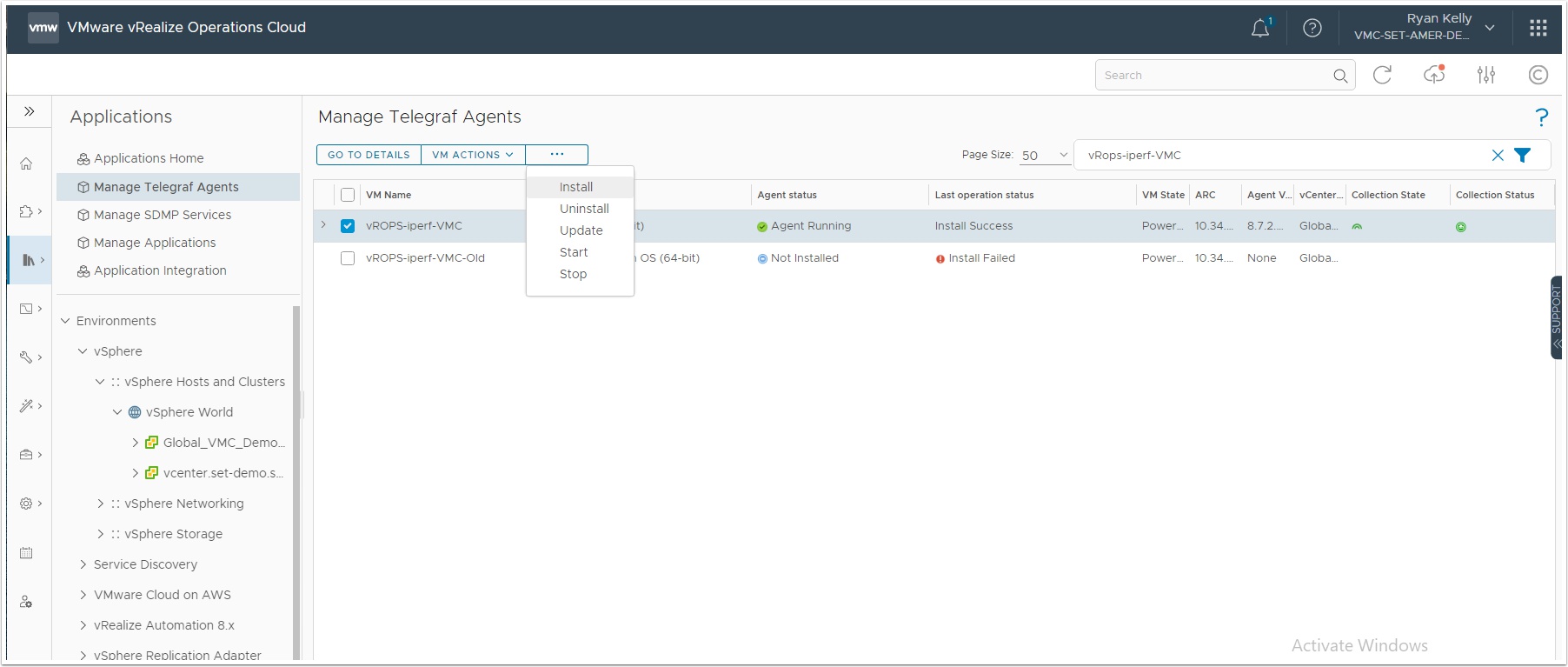
First, make sure you successfully install the Telegraph Agent on the Linux VM
Notice on my VM the agent is intalled, if not click the … icon and install it.
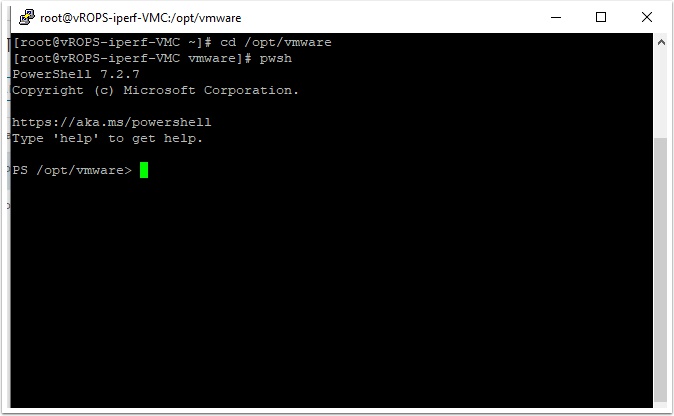
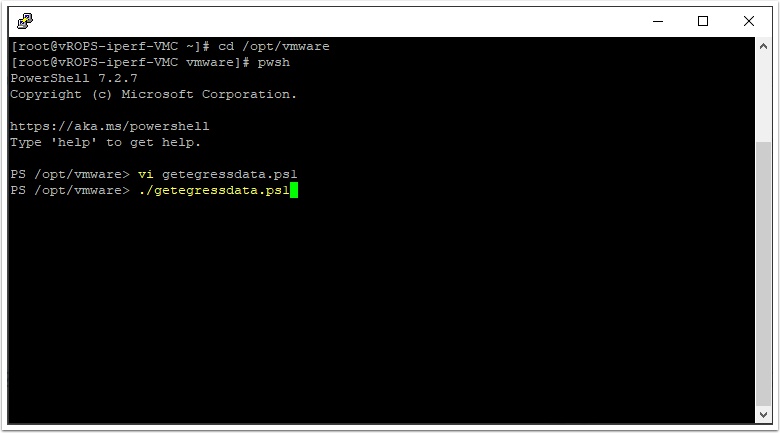
Login to the Linux VM so we can configure the scripts
Change to a folder where you can store your files
cd /opt/vmware
Make sure powershell for Linux is running by typing the following
pwsh
If you don’t have Powershell for Linux installed it’s easy, instructions are here: https://learn.microsoft.com/en-us/powershell/scripting/install/install-rhel?view=powershell-7.2
This integration is using a PowerCLI cmdlet that William Lam created and blogged about, please go to the following post and make sure you can complete the commands before proceeding. This guide is not meant to augment the work that William has done.
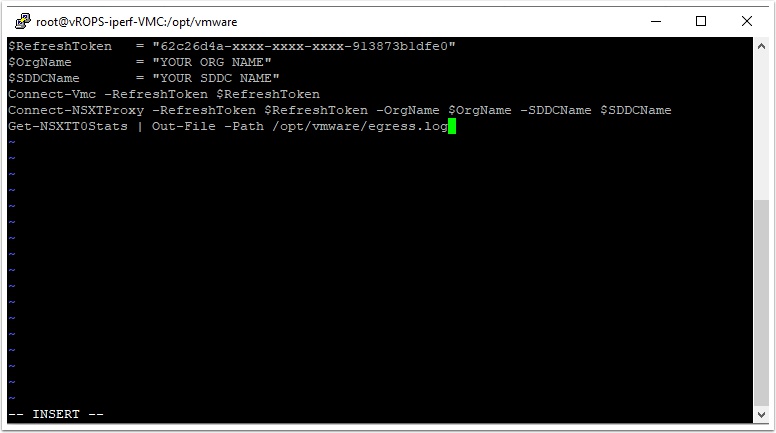
Create the following file and save it as getegressdata.ps1
vi getegressdata.ps1
Press i to insert
Paste the following changing the refresh token, OrgName and SDDC name to yours
$RefreshToken = "62c26d4a-xxxx-xxxx-xxxx-913873b1dfe0" $OrgName = "YOUR ORG NAME" $SDDCName = "YOUR SDDC NAME" Connect-Vmc -RefreshToken $RefreshToken Connect-NSXTProxy -RefreshToken $RefreshToken -OrgName $OrgName -SDDCName $SDDCName Get-NSXTT0Stats | Out-File -Path /opt/vmware/egress.log
Press Esc key
Hold Shift and at the same time press Z twice to save it
Note: This only runs the script one time and generates a log. You will need to create a cron job to run this regularly. Once daily would be my suggestion as this command itself will generate egress. See here to setup a Cron job.
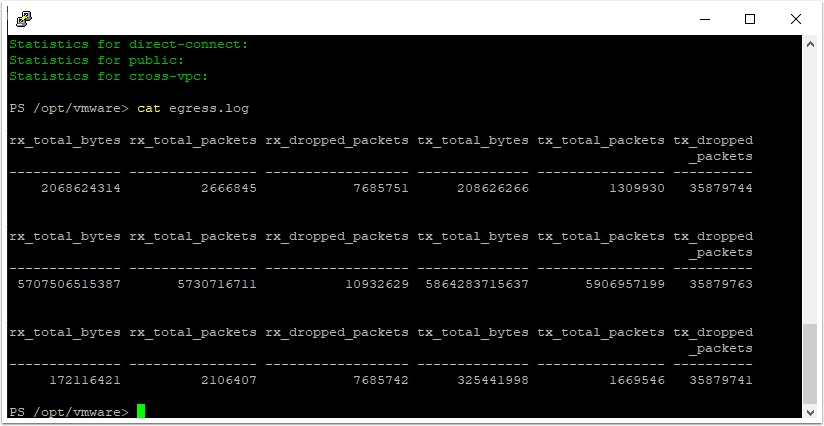
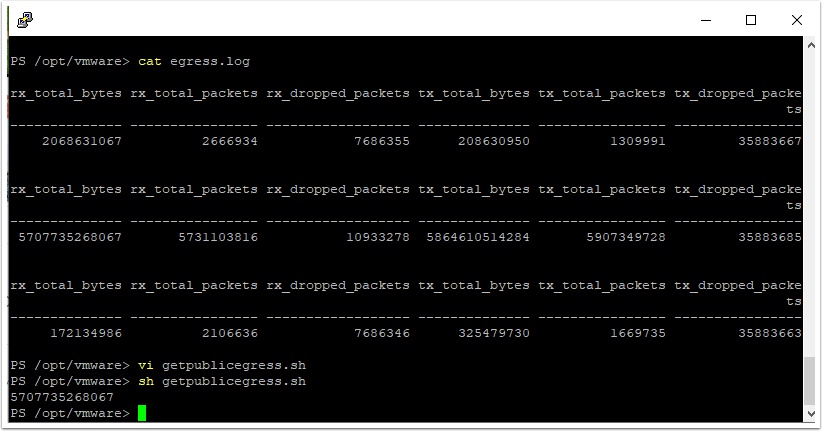
Once the script runs, type the following to view the log it created
cat egress.log
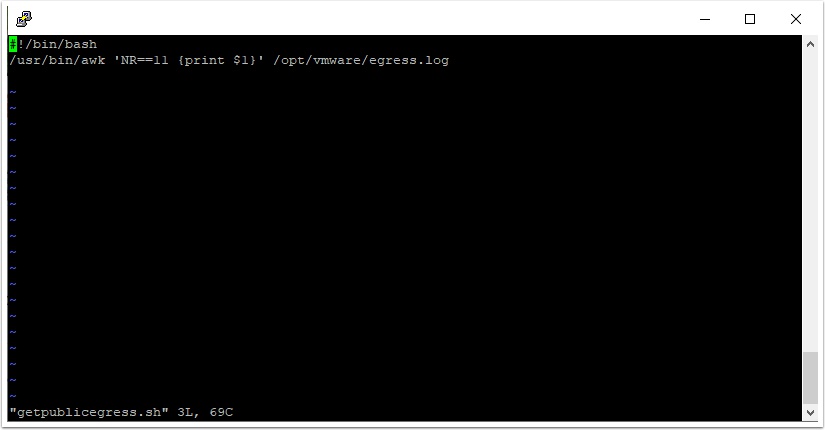
Ok, so now that we have the data let’s create the script that Aria Operations will use to display the Dashboard, create a file named getpublicegress.sh
vi getpublicegress.sh
Press i to enter insert mode
Paste the following:
#!/bin/bash
/usr/bin/awk 'NR==11 {print $1}' /opt/vmware/egress.log
Press Esc key
Hold Shift and press Z twice to save
Notice that NR is the line where the Public bytes are and Print $1 means the first text there. If you wanted to create separate scripts to monitor the Direct Connect and Cross VPC just create two more scripts that find the bytes data.
Run the script with the following to test that you are gettig the right number as output
sh getpublicegress.sh
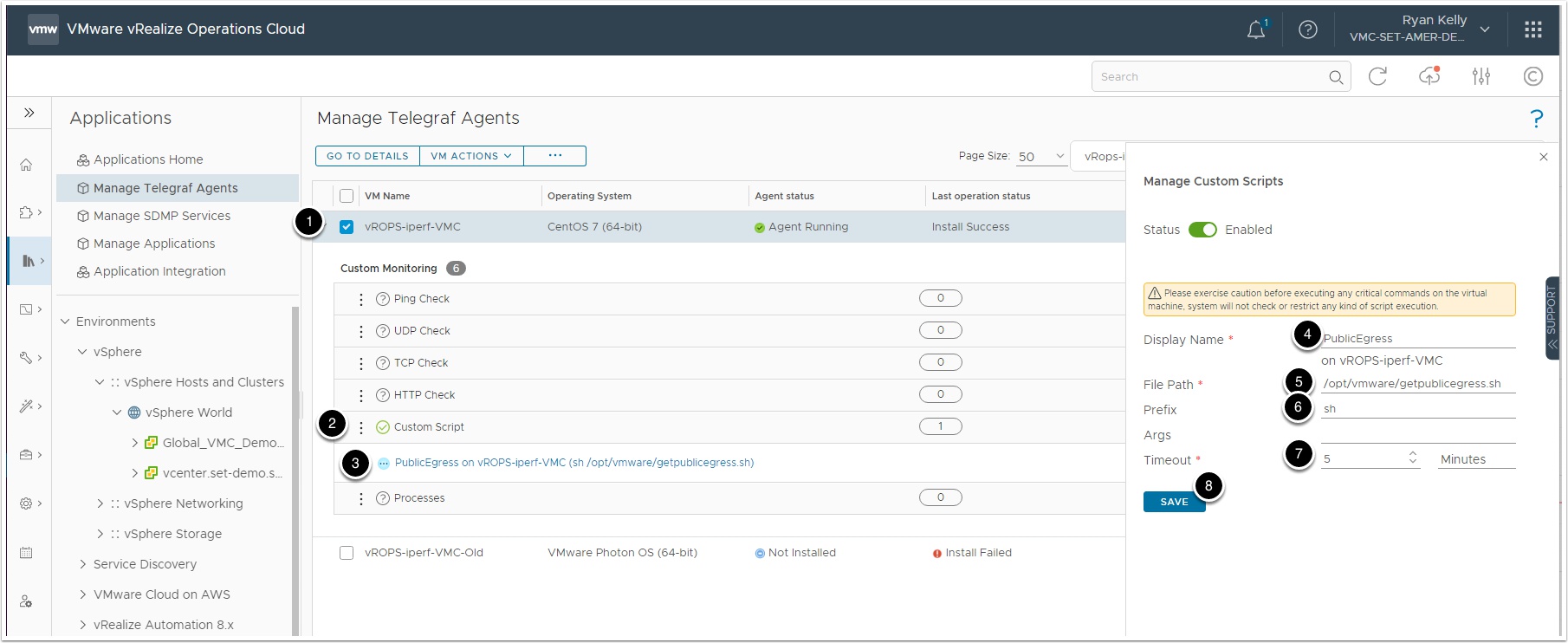
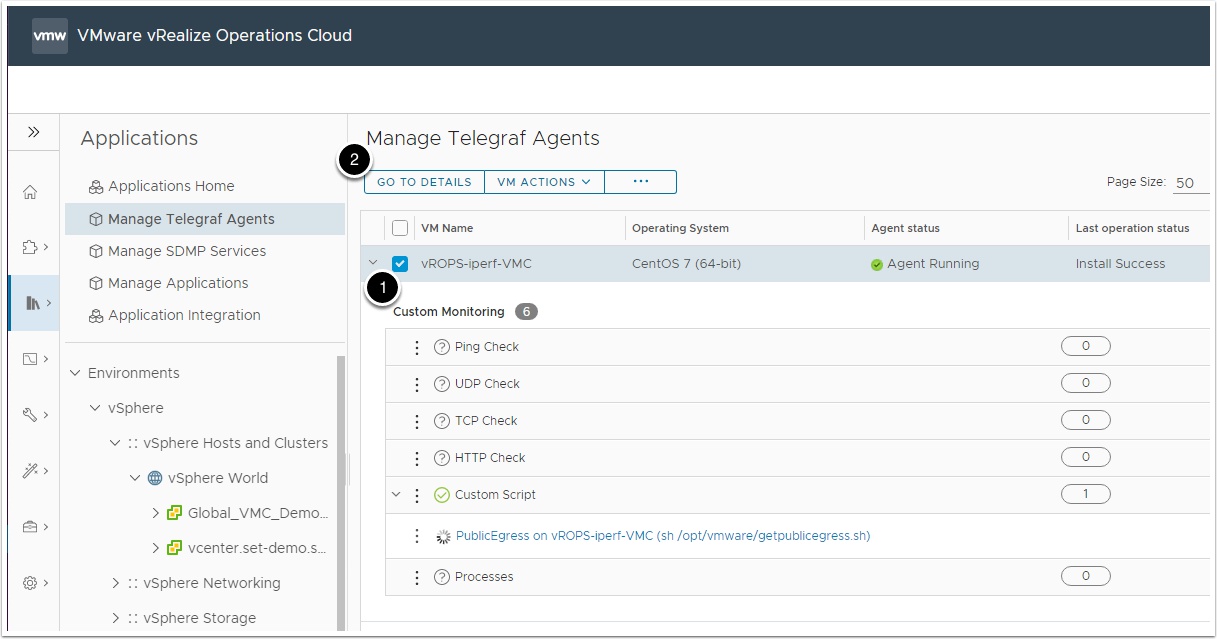
Now add the custom script back in Aria Operations (Formerly vRealize Operations)
- Click the drop down
- Click Custom Script
- Click to add new Custom Script
- Enter a Display name
- enter the file path to the script we just created
- enter sh as the prefix
- Set an interval of how often you want it to run
- Click Save
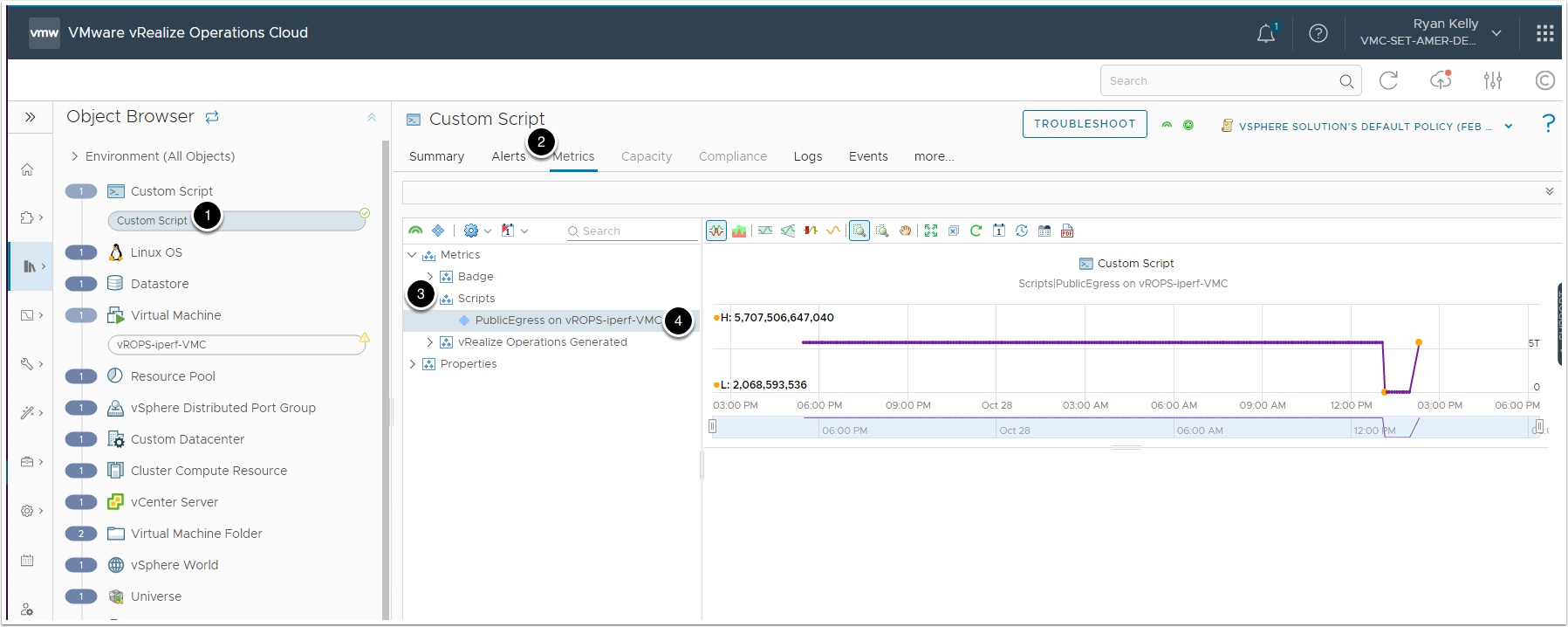
View the metric being collected from your custom script
- Click Custom Script
- Click Metrics
- Click the scripts drop down
- Double Click the Script we just created

x6hn0w