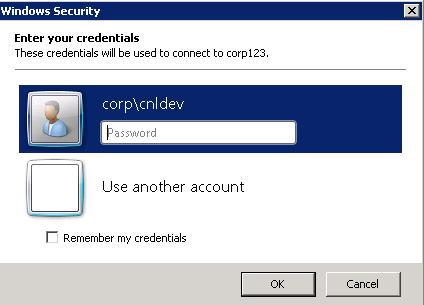
This guide details how to add the requester account to the local administrators group of the newly provisioned VM. You could also modify this to add them to power user or use a property set to have a drop down menu to select a group to add as well. It is up to you as this is meant to be a building block for so much more. In this example I am adding them to local administrator. This was tested with vCAC 6 but should also work with 5.2. For 5.2 you would need to use the 5.2 guest agents.
This guide requires that you already have vCAC installed and configured to provision to vSphere. You will also need to have a Windows Template with the Guest agent installed and configured. You can follow my guide here. Make sure the Windows VM is provisioning correctly and joining the AD domain.
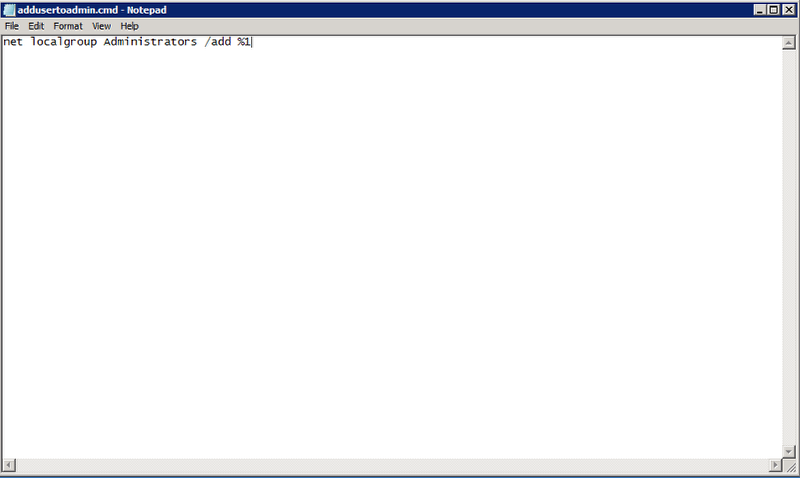
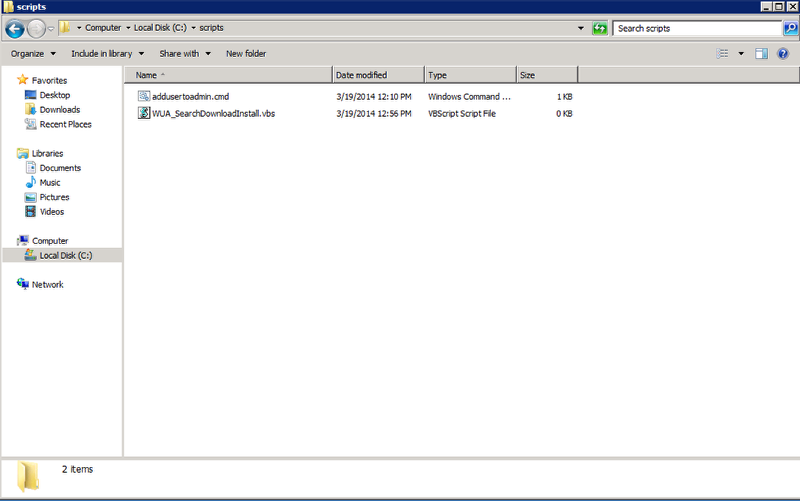
Step 1: Power on your base Windows Template VM in vCenter, login and create a new text file with the following line and save it as addusertoadmin.cmd to a folder named scripts on the C: drive of the Windows Server (Make sure the file gets saved as type Windows Command Script)
net localgroup Administrators /add %1
It should look like this when you are done. Shut down the VM and convert back to template or create a new snapshot if you are using linked clone. (Remember you will also need to perform an inventory data collection in vCAC and edit the Windows blueprint to point to this new snapshot)
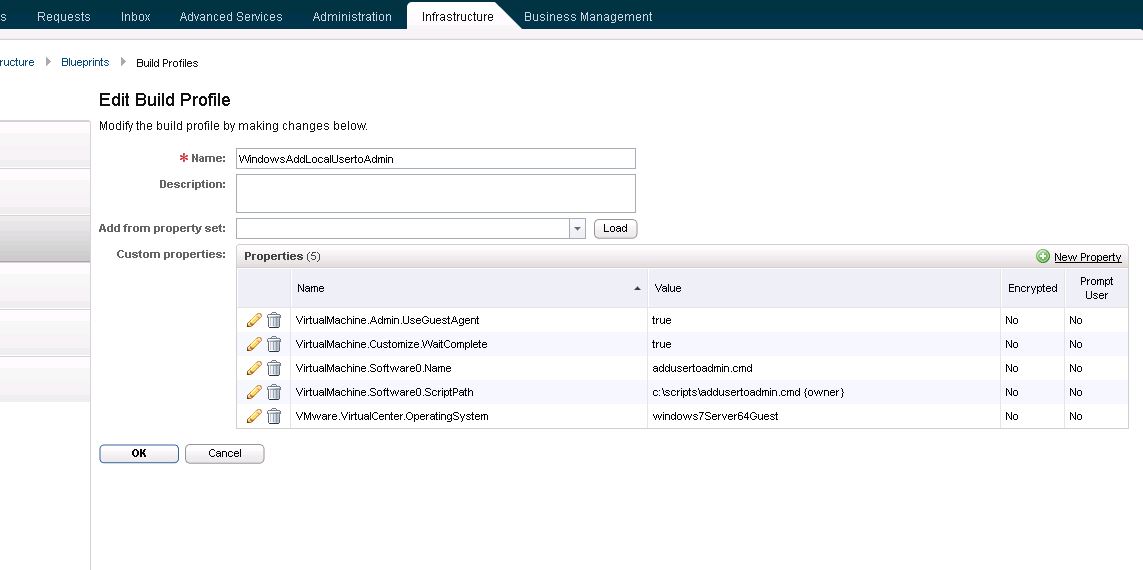
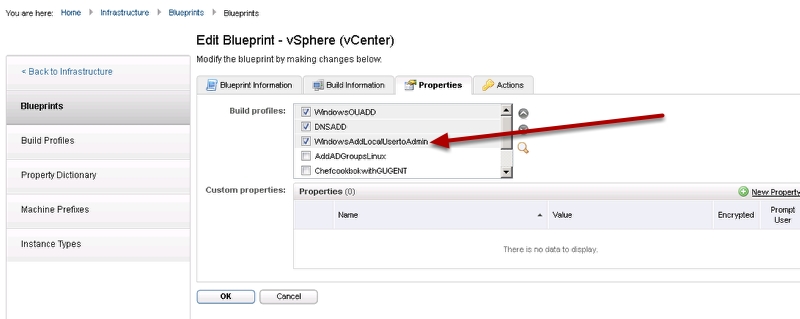
Step 2: Now we will need to create a new build profile with the custom properties that we need to run the guest agent and the script we created (See below image to copy and paste this into your system)
Copy and Paste Text for your convenience:
VirtualMachine.Admin.UseGuestAgent true
VirtualMachine.Customize.WaitComplete true
VirtualMachine.Software0.Name addusertoadmin.cmd
VirtualMachine.Software0.ScriptPath c:\scripts\addusertoadmin.cmd {owner}
Pingback: How to Create a vCAC 6 Guest Agent Windows Template | VMtoCloud.com
Hi Ryan,
Excellent use case that highlights the extensibility and power of vCAC. We have implemented this use case earlier in the year in vCAC 5.2 for a client and from our experience of it, it seems that the {Virtualmachine.admin.owner} property is not accessible to the vCAC guest agent even though it does appear in it’s log files. Our workaround was to use the {Owner} property instead and this worked to the same effect. not sure why this is the case but thought it might be a useful piece of info in case anyone else had the same difficulty
Thanks
Donal
Hi Donal,
Thanx for the tip. I updated the post with {owner} instead. The Linux guest agent also has this requirement.
I’d also like to clarify that {owner} does not work but {Owner} does.
Confirmed {Owner} works and {owner} doesn’t work in vCAC 6.0.1.
Pingback: vCAC 6 Lessons Learned | JP Tech Blog
Hi Ryan, excellent post! I had to adjust the variable in my .cmd file for it to work.. i.e., “net localgroup Administrators %1 /add” and I also used {Owner} with capital “O” instead of a lower case as Jay pointed out. Also, how would you handle a use case where an application binaries are already staged on a VM, it just needs to be kicked off as part of a post provisioning action?
Thanks!
Tony
Hi Tony,
You have two options, you could add an additional line to the .cmd file to kick off the binaries. You would also need to add a wait timer to the vCO workflow to pause the workflow long enough for the binaries to install. This will ensure that your installation finishes before the VM is handed off to the requester. You don’t want the requester to possibly interrupt your install. You could also accomplish this with vCAC guest agent. The agent has timing built in to allow the scripts to execute and finish before handing off the machine to requester. Here is a link to information on how to use the guest agent. http://dailyhypervisor.com/vcloud-automation-center-vcac-5-1-executing-scripts-with-the-windows-guest-agent/
Hi Ryan, thanks for the tip, that’s exactly what I was looking for. :))
Thanks Kevin, excellent article. I have followed the same steps on vCAC 6.1 however the request fails and I see the following errors in the VCAC for IaaS VM
Exception has been thrown by the target of an invocation. Inner exception: The transaction is in doubt. Base Exception: The wait operation timed out
HI AP,
It sounds like the Guest agent in the Windows VM is not calling back to the IaaS box. This could be a few issues. The cert for the IaaS box may not be configured correctly on the Windows VM. You may need to walk through the Guest agent install again. Other issue is if you are using Windows Server 2012 for your IaaS box you will also need to disable TLS 1.2 and reboot that server. Instructions here http://support.microsoft.com/kb/245030
Hey Ryan, do you have any experience using a space in a variable with gugent? It appears no matter how I try to quote it, it truncates all after the space. It may be that you can’t use spaces. I am passing %1 just as you are but %1 has a space in it.
Hi Mike,
I have experience using white spaces but no success as it is not yet supported with Windows or Linux Gugent. There is a feature request in by yours truly!! With that said I did manage to find a workaround using vCO and the Guest scripts package. Check out this guide https://www.vmtocloud.com/docker-as-a-service-in-vravcac-part-2-installpullandrun/
Hi Guys,
Just had this challenge myself with a 6.01 environment and I was able to quote the value with the space in it. I’m passing the Properties to a cmd file that then passes them on to a powershelgl call. I found that enclosing the value in “” in the Build Profile property didn’t work but that vCAC automatically seems to do this when it processes the value (you can check the properties attached to the machine during/after provisioning to see this Infrastructure > Machines > Managed Machines).
If I configure the value without quotes in the Build profile then as stated vCAC passes it onto the script call in double quotes ; I then enclose the %1 in single quotes to have the value continue to be passed along to powershell. for example:
powershell.exe -noprofile -executionpolicy bypass -command “& ‘c:\dummy\test.ps1’ ‘%1′”
this seems to work for me at the moment.
HTH
Donal